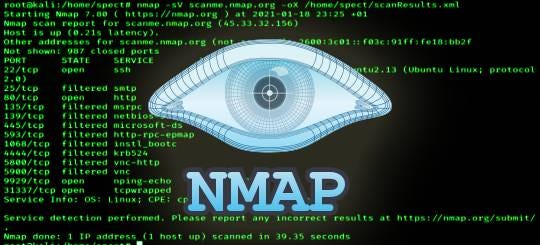
MSSQL for Pentester: Nmap
Requirement
Attacker: Kali Linux (NMAP)
Target: Windows 10 (MS SQL Server)
Nmap is a collection of Lua-based NSE scripts that conduct authentication and unauthenticated penetration testing on MS-SQL port 1433. The NSE script for MS-SQL may be identified using the instructions below.

Enumerating version
This Script will attempt to determine configuration and version information for Microsoft SQL Server instances.

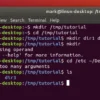
Credential Brute Force
Performs brute-force password auditing against Ms-SQL servers and connection timeout (default: “5s”). All we need are dictionaries for usernames and passwords, which will be passed as arguments.
In the image you can observe that we had successfully retrieve credentials for three users:

Execute SQL Query
Once you have retrieved the login credential use these credentials in the NMAP script to execute MS –SQL query. Given below will try to execute certain query “sp_database” against Microsoft SQL Server.
Specified query “sp_databases” is part of record Stored Procedures and dump a list of database names from an instance of the SQL Server.

NetBIOS Enumeration
Given below NMAP script will enumerate information from remote Microsoft SQL services with NTLM authentication enabled.
Sending an MS-TDS NTLM authentication request with an invalid domain and null credentials will cause the remote service to respond with an NTLMSSP message disclosing information to include NetBIOS, DNS, and OS build version.

MS-SQL Password Hash Dump
The following command will dump the password hashes from an MS-SQL server in a format suitable for cracking by tools such as John-the-ripper. To do so, the user needs to have the appropriate DB privileges.
From the given image you can observe that it has dumped the hash value of passwords of the user: sa which we have enumerated above.

Command Excecution
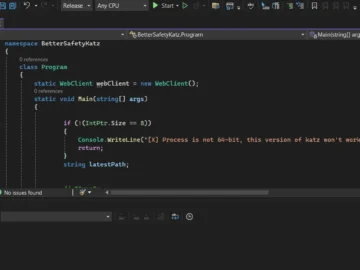
The xp_cmdshell is a function of Microsoft SQL Server that allows system administrators to execute an operating system command. By default, the system disables the xp_cmdshell option. The NMAP script will attempt to run a command using the Microsoft SQL Server command shell if it finds that xp_cmdshell is enabled on the targeted server.
From the depicted image you can perceive the output for the “net user” command.

Test Empty Password Login
If the administrator of Microsoft-SQL Server left the password blank for login, the attacker can direct login into the database server; as shown in the image below, we are investigating the property of a user’s account “sa.”

Following NMAP script will try to authenticate to Microsoft SQL Servers using an empty password for the sysadmin (sa) account.
We had successfully logged in with user: sa and an empty password, as you can see in the screenshot below.

Enumerate Database Tables
The following command will attempt to fetch a list of tables from inside the Microsoft SQL server bypassing login credentials as an argument through Nmap script.












 HACK RF RADIO AND NET HUNTER PHONE
HACK RF RADIO AND NET HUNTER PHONE



 USING WIGLE + WIFITE + ALFA ADAPTER
USING WIGLE + WIFITE + ALFA ADAPTER
 Daily practice and real-time application is key to perfection
Daily practice and real-time application is key to perfection