A Guide to SQL Injection Attacks: Hackers Don’t Want You to Know This
Imagine your website as a big toy box filled with treasures — like user info, passwords, or blog posts — and you’ve got a robot helper (your database) that grabs the toys you ask for.
But what if a clever thief tricks the robot into handing over toys they’re not supposed to touch?
That’s what SQL injection is: a sneaky way hackers mess with your website’s database to steal, change or even delete your treasures.
In this blog post, we’ll explain SQL injection in easy English, walk you through the different ways hackers attack and share simple tips to keep your website safe.
Got questions about what is SQL Itself? Check out the below blog post to learn more. 👇
Why Everyone Should Learn SQL (And How to Start)
Imagine having the key to unlock the secrets hidden in your organization’s data. No more waiting for someone else to…
What Is SQL Injection?
Your website often uses a database to store important stuff, like a list of users or blog posts. To talk to the database, your website uses a language called SQL (Structured Query Language).
For example, if someone visits a blog post on your site, the URL might look like this:
https://yoursite.com/blog?id=1
The website sends an SQL query to the database to get that post:
SELECT * FROM blog WHERE id = 1 AND private = 0 LIMIT 1;
This tells the database, “Give me the blog post with ID 1, but only if it’s public (not private), and just one result.”
Everything seems fine — until a hacker gets involved.
If your website doesn’t check what people type into things like URLs or forms, a hacker can add their own SQL code. This is called SQL injection. They can trick the database into doing things it shouldn’t, like showing private posts or stealing data.
For example, a hacker might change the URL to:
https://yoursite.com/blog?id=2;
This changes the query to:
SELECT * FROM blog WHERE id = 2; -- and private = 0 LIMIT 1;
The ; ends the query early, and — ignores the rest, skipping the private = 0 check. Now the hacker can see a private post (ID 2) they shouldn’t have access to. It’s like giving the robot helper a fake instruction to grab a toy from a locked box!
The Different Ways Hackers Use SQL Injection
Hackers have a few tricks to attack with SQL injection. Let’s break them down in a simple way so you can understand how they work and why they’re dangerous.
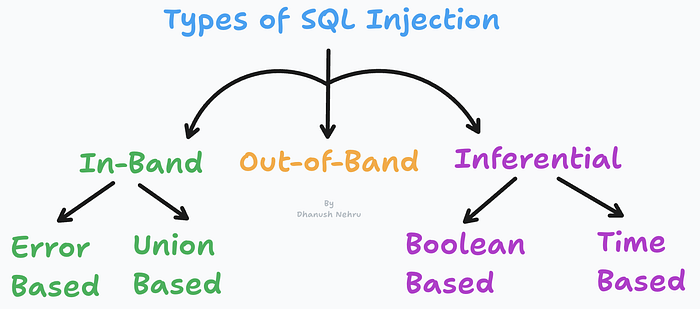
1. In-Band SQL Injection: The Easy Sneak
This is the simplest way hackers attack. They use the same place — like a search bar or URL — to sneak in their trick and see the results right away.
Error-Based SQL Injection:
- Hackers make the database mess up on purpose to spill secrets. For example, they might try:
SELECT * FROM users WHERE id = 1 AND 1=CONVERT(int, (SELECT @@version));
- This query tries to turn the database’s version (like “MySQL 8.0”) into a number, which it can’t do. The database might throw an error that says, “Error: MySQL 8.0.” That tells the hacker what kind of database you have, so they can plan more attacks. It’s like the robot helper accidentally telling the thief where the key to the toy box is hidden!
Union-Based SQL Injection:
Hackers use a command called UNION to grab extra toys from other boxes. Let’s say the original query is:
SELECT name, email FROM users WHERE id = 1;
A hacker might add:
SELECT name, email FROM users WHERE id = 1 UNION ALL SELECT username, password FROM admin;
- This combines the results, so the hacker gets not just the user’s name and email but also usernames and passwords from the admin box. It’s like asking the robot for one toy but sneaking a peek at a secret treasure chest too.
2. Blind SQL Injection: The Guessing Game
Sometimes, the website doesn’t show errors or data directly, so hackers have to guess what’s in the database by watching how the website behaves. This is called blind SQL injection, and it’s trickier but still dangerous.
Boolean-Based Blind SQL Injection:
- Hackers ask yes-or-no questions and watch the website’s reaction. For example:
SELECT * FROM users WHERE id = 1 AND 1=1;
- This is true, so the website might show a normal page. Then they try:
SELECT * FROM users WHERE id = 1 AND 1=2;
- This is false, so the website might show “No results” or act differently. By noticing these changes, hackers can guess things like, “Is there a user named ‘admin’?” It’s like playing a guessing game with the robot helper — asking, “Is this toy in the box?” and watching its reaction.
Time-Based Blind SQL Injection:
- If the website doesn’t give visual clues, hackers use time to figure things out. They might send:
SELECT * FROM users WHERE id = 1; IF (1=1) WAITFOR DELAY '00:00:05'--;
- This tells the database, “If 1=1 (which is true), wait 5 seconds before answering.” If the website takes 5 seconds to load, the hacker knows the answer is “yes.” They can use this to ask questions like, “Does the admin’s password start with ‘p’?” It’s like asking the robot, “If I’m right, take a long nap before answering!”
3. Out-of-Band SQL Injection: The Secret Messenger
This trick is less common but super sneaky. If hackers can’t get results through the website, they make the database send the info straight to their own computer, like sending a secret message over the internet (using something called HTTP or DNS). For example, they might trick the database into sending stolen passwords to their server. This only works if the database can send these messages, but when it does, it’s a big win for the hacker. It’s like the robot helper mailing the toys directly to the thief’s house!
Why SQL Injection Is a Big Deal
SQL injection isn’t just a small problem — it can cause huge trouble. Hackers can use it to:
- Steal Treasures: They can take sensitive stuff like user names, passwords, or credit card info.
- Mess with Things: They might change data, like making a private blog post public or changing someone’s account balance.
- Break Everything: They can delete your entire database, wiping out all your toys in one go.
- Take Over: In the worst cases, they might use stolen info to log in as an admin and take control of your website.
It’s like a thief not just stealing your toys but also breaking them, rearranging the toy box, or even locking you out of your own playroom!
How to Keep Your Website Safe
Don’t worry — you can stop SQL injection with some easy steps. Here’s how to keep your website’s toy box safe:
- Check Everything People Type: Make sure your website double-checks what people put into forms or URLs. If it expects a number (like an ID), don’t let it accept random SQL code. It’s like making sure the robot helper only listens to real instructions.
- Use Prepared Statements: Instead of putting user input straight into your SQL query, use a “prepared statement.” This is like giving the robot a pre-written note that can’t be changed, so hackers can’t sneak in their own tricks.
- Limit the Robot’s Power: Make sure your database user (the one your website uses) can only do what it needs to — like reading data, not deleting everything. It’s like telling the robot, “You can only hand out toys, not break them.”
- Hide Mistakes: Don’t let your website show detailed database errors to users. Hackers can use those to learn about your database. Instead, show a simple message like, “Oops, something went wrong.”
- Stay Updated: Keep your database software (like MySQL) and website code up to date. Updates often fix holes that hackers might use to sneak in.
Why Understanding SQL Injection Matters
Each type of SQL injection has its own strengths and challenges. In-band attacks (like error-based and union-based) are easy for hackers to do but also easy to spot because they’re noisy.
Blind attacks (like boolean-based and time-based) are harder to pull off and need lots of guesses, but they work even if your website doesn’t show errors. Out-of-band attacks are rare but super effective if the database can send secret messages to the hacker.
By understanding these tricks, you can protect your website and keep your data safe. Whether you’re a website owner, a developer, or just curious, knowing about SQL injection helps you stop hackers before they cause trouble.















 HACK RF RADIO AND NET HUNTER PHONE
HACK RF RADIO AND NET HUNTER PHONE



 USING WIGLE + WIFITE + ALFA ADAPTER
USING WIGLE + WIFITE + ALFA ADAPTER
 Daily practice and real-time application is key to perfection
Daily practice and real-time application is key to perfection