Breaking News
2025-07-28 How to Hack Any WAF with Just One cURL Command
2025-06-19 How to easily install Kali Linux 2025.1a
2025-05-22 Hacking prerequisites : An introduction to computer networking
2025-05-22 Pentesting Active Directory: The Ultimate Methodology Guide
2025-05-21 Tor Oniux Tool Offers Anonymous Linux App Traffic
Newest Hacks
The only way to understand HTTP in 2025
HTTP (Hyper Text Transfer Protocol) is basically a client-server protocol, wherein the client (web browser) makes a request to the...
10 Time-Saving Linux Automation Scripts Every User Should Know
Automation is one of the greatest strengths of Linux, and with just a few scripts, you can save time and...
Page 1 of 24
How to Hack Any WAF with Just One cURL Command
Web Application Firewalls (WAFs) like Cloudflare, Akamai, and AWS Shield are supposed to stop hackers dead in their tracks. But what if I...
How to easily install Kali Linux 2025.1a
Kali Linux 2025.1a released with 1 new tool, annual theme refresh Kali Linux has released version 2025.1a, the first version...
Hacking prerequisites : An introduction to computer networking
Hacking prerequisites : An introduction to computer networking Why do we need networking for ethical hacking? Before you jump into...
Page 1 of 24
How to get the best wordlists for hacking
Wordlists for Pentester Introduction Ever since the evolution of Penetration Testers has begun, one of the things we constantly see...
How to easily install Kali Linux 2025.1a
Kali Linux 2025.1a released with 1 new tool, annual theme refresh Kali Linux has released version 2025.1a, the first version...
The Best Practical SQL Injection Exploitation Cheat Sheet
Practical SQL Injection Exploitation Cheat Sheet Introduction SQL Injection (SQLi) remains one of the most dangerous vulnerabilities in web applications,...
Page 1 of 24
BUY A GOOGLE PIXEL PHONE FOR PEN TESTING

DONT WASTE TIME BUYING iPHONE OR GALAXY PHONES THAT HAVE SECURITY FEATURES THAT DON’T ALLOW OEM UNLOCKING.
THIS FEATURE ENABLES YOU TO ROOT YOUR DEVICE WITH MAGISK AND ENABLES TO INSTALL NETHUNTER AND UNLEASH YOUR FULL PENETRATION TESTING POTENTIAL.
Most Liked Hacks
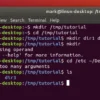
Mastering the basics of linux the best way possible
Beginner Commands 1. CTRL + ALT + T It is not exactly a command but an awesome shortcut. You can...
How hackers can easily steal your passwords
In this article, you’ll learn how hackers steal passwords using a fake login page. Hackers can steal your password through...
The best detailed guide to rustscan for 2025
“In the realm of cybersecurity, Rustscan network scanner plays a vital role in reconnaissance and vulnerability assessment. Among the array of options...
Page 1 of 24
HACKING GEAR FOR BEGINNERS
 HACK RF RADIO AND NET HUNTER PHONE
HACK RF RADIO AND NET HUNTER PHONE
THESE BEGINNER GADGETS WILL GIVE YOU A FOUNDATION INTO HACKING, AND HOW TO HACK ON THE GO. USING SDR IN ORDER TO EXPERIMENT WITH RADIO FREQUENCIES AND USING NETHUNTER TO EXPERIMENT WITH WEB APPLICATION, REMOTE VIEWING, AND PASSWORD AND PHISHING ATTACKS.
WIFI PINEAPPLE HUNTING

PLACING ROUGE NETWORKS IN CAMPING GEAR IN ORDER TO EXTRACT PASSWORDS.
IN THIS PARTICULAR ATTACK ROUGE NETWORKS MIMIC WIFI NETWORKS AND ENABLE THE ATTACKER TO EXTRACT EMAIL AND PASSWORD INFORMATION.
Latest Hacks
The only way to understand HTTP in 2025
HTTP (Hyper Text Transfer Protocol) is basically a client-server protocol, wherein the client (web browser) makes a request to the...
15 Linux commands programmers should know
Most programmers barely scratch the surface, relying on basic Linux commands while overlooking features that could make their lives exponentially...
How to Use Kali Linux for OSINT Investigations
How to Use Kali Linux for OSINT Investigations Let’s Get Started! 1. Setting Up VirtualBox Download VirtualBox by clicking here, or...
Page 1 of 24
COSMIC COMMUNICATOR + RASPBERRY PI + TP LINK V1

THIS ATTACK ENABLES THE ATTACKER TO REMOTELY AND DISCRETELY DEAUTHORIZE DEVICES OFF OF A NETWORK AND ENABLING THE ATTACKER TO VIEW WEBSITE INFORMATION AS WELL AS INTERCEPTING PHONE CALLS.
WAR DRIVING
 USING WIGLE + WIFITE + ALFA ADAPTER
USING WIGLE + WIFITE + ALFA ADAPTER
IN ORDER TO TEST WIFI NETWORKS AND INTERCEPT HTTPS TRAFFIC FROM UNSUSPECTING TARGETS IN ORDER TO TEST NETWORK SECURITY
Recent Posts
Use linux in order to extract information and become self sufficient

Nighttime hacking is the best time to extract information in CQC
THERE IS NO NEED TO GO TO ANOTHER WEBSITE !
THIS IS THE BEST WEBSITE FOR HACKING AND LOCKING PICKING AS WELL AS REPROGRAMMING YOU MIND AND SOUL INTO BEING COMPLETELY SELF-SUFFICIENT.
pistol accuracy + lockpicking + password hacking
 Daily practice and real-time application is key to perfection
Daily practice and real-time application is key to perfection
Copyright © 2026 melanatedspy












Recent Comments