DNS Rebinding in Kali Linux: A Guide for ALL Hackers
Welcome back, MelanatedSpy! Today, we’re diving into the world of DNS rebinding attacks, a fascinating technique that exploits how browsers and DNS resolvers handle domain names. By the end of this guide, you’ll understand what DNS rebinding is, how it works, and how to set it up in Kali Linux.
What is DNS Rebinding?
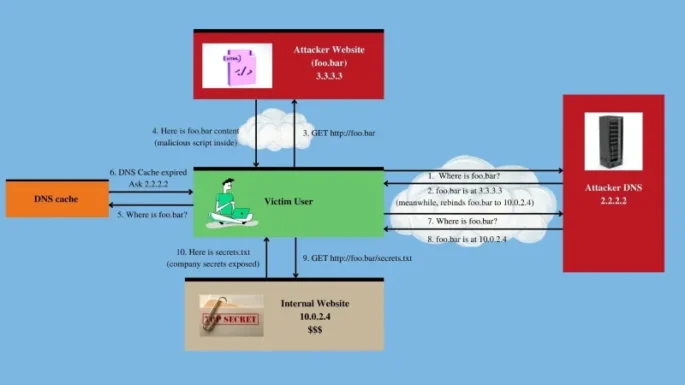
DNS rebinding is a technique that allows an attacker to bypass the same-origin policy in web browsers. It tricks a victim’s browser into executing malicious scripts on a different domain (usually an internal network) by manipulating DNS responses.
How It Works:
- The attacker sets up a malicious DNS server and a web server.
- The victim visits the attacker-controlled website.
- The attacker’s DNS server resolves the domain name to the attacker’s server initially.
- After a short time, the DNS server resolves the same domain name to an internal IP address (e.g.,
192.168.1.1), allowing the attacker to interact with devices on the victim’s local network.
Why Use DNS Rebinding?
DNS rebinding can be used for:
- Internal Network Scanning: Access devices behind a firewall.
- Exfiltration: Extract sensitive data from internal systems.
- Exploitation: Exploit vulnerabilities in internal services.
Setting Up a DNS Rebinding Attack in Kali Linux
1. Install the Necessary Tools
Kali Linux provides several tools for DNS rebinding. One popular tool is Rebind.
- Install Rebind:
sudo apt update
sudo apt install rebind
2. Configure the Rebind Tool
Rebind is a DNS server designed specifically for DNS rebinding attacks.
- Edit the Configuration: The configuration file is usually located at
/etc/rebind/rebind.conf. Modify it to include your target IP address and domain.Example:domain=example.com
ip=192.168.1.1
ttl=1
domain: The domain name you control.ip: The internal IP address to which you want to rebind.ttl: Time-to-live, which determines how quickly the DNS record changes.
3. Start the Rebind Server
Run the Rebind server to start serving malicious DNS responses.
sudo rebind
4. Set Up a Malicious Web Server
You’ll need a web server to host the malicious payload. Use Python’s HTTP server module for simplicity:
sudo python3 -m http.server 80
5. Craft the Malicious Payload
Create a JavaScript payload to interact with the target’s internal network. For example, a script to scan open ports:
<script>
var img = new Image();
img.src = "http://192.168.1.1:8080";
</script>
Save this payload in an HTML file and serve it from your web server.
6. Test the Attack
- Host your malicious domain (e.g.,
example.com) on the Rebind DNS server. - Send the victim a link to your malicious domain.
- Monitor the requests to your server and the interaction with the internal network.
Ethical Considerations
As always, MelanatedSpy, it’s important to emphasize that DNS rebinding attacks should only be performed in authorized environments. Use this technique responsibly and ensure you have explicit permission before conducting any tests.
Advanced Tips for MelanatedSpy’s Readers
- Automate with Tools: Use tools like
dnscheforbettercapfor more advanced DNS manipulation. - Bypass Protections: Explore ways to bypass DNS rebinding protections, such as browser mitigations or firewall rules.
- Combine with Other Attacks: Pair DNS rebinding with XSS or CSRF for more complex exploits.
Conclusion
DNS rebinding is a powerful technique that demonstrates the importance of securing internal networks and DNS configurations. By mastering this attack, you’ll gain a deeper understanding of how to protect against it.















 HACK RF RADIO AND NET HUNTER PHONE
HACK RF RADIO AND NET HUNTER PHONE



 USING WIGLE + WIFITE + ALFA ADAPTER
USING WIGLE + WIFITE + ALFA ADAPTER
 Daily practice and real-time application is key to perfection
Daily practice and real-time application is key to perfection